Why WhatsApp privacy and security matter to businesses
When customers message your brand on WhatsApp, they’re not just chatting - they’re sharing identities, intent, and often sensitive details that drive revenue and service outcomes. Treating privacy as a first‑class product requirement is how you protect customers, maintain compliance, and keep your WhatsApp channel performing at its best. As an official WhatsApp Business API partner, Trikon helps brands operationalize privacy by design - so you can scale conversations with confidence.
What this guide covers
Practical, product-led playbook for WhatsApp privacy: encryption basics, consent and lawful messaging, data handling, retention, rights requests, and operational security.
Built for D2C, e‑commerce, service businesses, enterprises, and agencies using WhatsApp Business API/BSPs.
Why privacy is non-negotiable on WhatsApp Business
Sensitive conversations: orders, payments, support history, and personally identifiable information (PII) routinely flow through WhatsApp private messaging. Leaks here are high-risk.
Regulatory exposure: GDPR/UK GDPR, CCPA/CPRA, LGPD, PDPA, POPIA, and industry rules (e.g., PCI DSS, HIPAA overlays) can apply depending on your audience and use case.
Business impact: trust and brand equity, WhatsApp Quality Rating and deliverability, campaign ROI, and conversion rates all depend on clean consent and compliant data handling.
"The global average cost of a data breach reached $4.45 million in 2023." - Source
What counts as “whatsapp privacy,” “whatsapp private messaging,” and “whatsapp policies” in this context
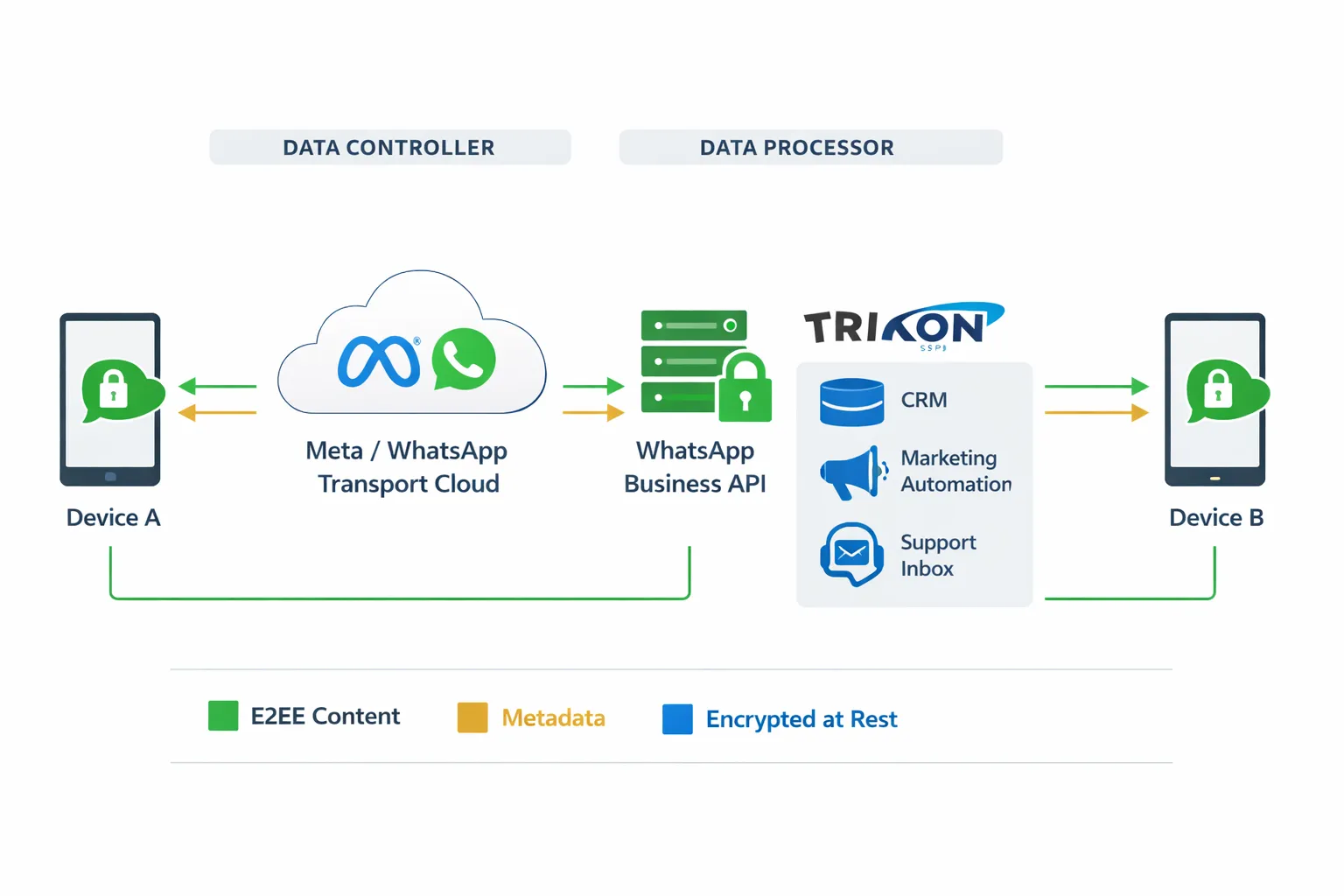
Encryption vs. controller duties: WhatsApp’s end‑to‑end encryption protects messages in transit and at rest on devices. Your responsibilities begin the moment messages reach your systems or your Business Solution Provider (BSP). As the data controller, you must govern consent, lawful basis, retention, access, and subject rights.
The rules of WhatsApp vs. data protection law:
WhatsApp policies and rules cover template categories, opt‑in requirements for marketing, acceptable use, and sender behavior that affects Quality Rating and message deliverability.
Data protection law governs lawful basis (consent/contract/legitimate interest), explicit opt‑out, data minimization, purpose limitation, retention schedules, deletion, and auditability.
Practical translation: clear opt‑ins per channel, transparent disclosures, easy opt‑outs, minimal data capture, masked PII in logs, least‑privilege access, and documented retention with automated deletion.
Scope of this guide
Applies to the WhatsApp Business Platform (API), the WhatsApp Business App with integrations, and BSP‑hosted solutions such as Trikon.
Covers privacy across cloud hosting, vendor processing, agent desktops/inboxes, analytics, and cross‑border data transfers - especially when using Meta Cloud API or third‑party processors.
Focuses on scalable, product‑led controls you can implement in Trikon: policy‑aware broadcasts, consent and segmentation, secure shared inbox with role‑based access, encryption options, and automated retention to reduce risk while protecting growth.
Encryption, metadata, and the realities of WhatsApp Business (E2EE demystified)
WhatsApp private messaging is secured with end-to-end encryption (E2EE), but businesses still handle metadata and business-side storage that fall under both WhatsApp policies and data protection law. Here’s what’s truly private, what isn’t, and how to operationalize whatsapp privacy without hurting performance or compliance.
How WhatsApp end-to-end encryption (E2EE) works
Messages, media, voice notes, and calls are E2EE between devices. Only the sender and recipient devices hold the keys, so message content cannot be read in transit by WhatsApp or intermediaries.
“We can’t read your messages” in practice: WhatsApp LLC relays encrypted payloads for delivery and does not have the keys to decrypt message bodies. Delivery logic and rate limiting depend on metadata - not content.
"As always, your personal messages and calls are end-to-end encrypted. No one else, not even WhatsApp, can read or listen to them." - Source
What is encrypted vs. what isn’t for businesses
Content vs. metadata: E2EE protects message bodies (text, media, voice notes, calls). Metadata - like timestamps, phone numbers, message IDs, delivery status, and device signals - are not protected by E2EE and can be processed for routing, deliverability, analytics, and anti‑abuse.
Business-side storage: Once messages reach your WhatsApp Business API endpoint, inbox, or integrations (CRM, CS platform, data warehouse), transcripts and customer profiles live in your systems. That processing is governed by your lawful basis, retention rules, access controls, and security posture - not by WhatsApp’s encryption.
Hosting models and privacy implications
Meta‑hosted (Cloud API): Processing occurs on Meta infrastructure. Your organization is typically the data controller for customer data; Meta acts as a processor for transport/hosting of business communications. Cross‑border transfers and processor terms apply.
BSP‑hosted (e.g., Trikon): The BSP provides the WhatsApp Business Platform as a processor. Your organization remains the controller. Ensure the BSP contract covers sub‑processors, encryption‑at‑rest, access logging, and data residency where required.
Self‑hosted API: You manage the WhatsApp Business API client and stack. You are the controller, and your hosting provider (if any) is a processor. You own responsibility for security hardening, backups, monitoring, and lawful data flows.
Practical takeaway: E2EE protects content on the way to you. From your API endpoint onward, whatsapp policies and data protection rules (consent, opt‑out, minimization, retention, access) govern everything you store and process.
WhatsApp privacy messages for businesses: practical outcomes
Private messaging settings: Use disappearing messages and view‑once media to limit exposure for highly sensitive content. These are UX controls; they do not replace controller duties for retention and rights requests.
E2EE vs. retention and audits: E2EE doesn’t dictate how long your business keeps data. Design retention by purpose and legal basis. Enable audit trails (agent access, exports, sharing) without storing sensitive content longer than necessary.
Inbox and API hygiene: Align template policies, opt‑in language, and opt‑out flows with both WhatsApp rules and data protection law. Enforce least‑privilege access, encryption‑at‑rest for stored transcripts, and masked PII in logs.
What’s encrypted vs. what isn’t (at a glance)
Data category | Examples | E2EE in transit (Yes/No) | Visible to business systems (Yes/No) | Typical retention location (Device/WhatsApp infra/Business systems) | Notes |
|---|---|---|---|---|---|
Message body | Text content in chats | Yes | Yes | Device, Business systems | Decrypted on recipient device; stored in inbox/CRM if integrated - apply minimization/retention. |
Media attachments | Images, PDFs, invoices, receipts | Yes | Yes | Device, WhatsApp infra (temporary), Business systems | Temporarily stored (encrypted) for delivery/forwarding; avoid over‑retention in business tools. |
Voice notes | Voice messages | Yes | Yes | Device, Business systems | Treat as recordings containing personal data; define strict retention. |
Template variables | Name, order ID, ETA | Yes | Yes | Business systems | Variables are part of encrypted content; keep sensitive PII out of templates when possible. |
Message IDs & timestamps | Message IDs, sent/delivered/read times | No | Yes | WhatsApp infra, Business systems | Metadata drives routing/delivery and analytics - govern as personal data where identifiable. |
Phone numbers | Customer MSISDN, agent numbers | No | Yes | Business systems | Core identifier; requires lawful basis, opt‑out handling, and data quality controls. |
Device/IP metadata | IP, OS, device model, locale | No | No (by default) | WhatsApp infra | Typically not exposed to businesses via API; still personal data within WhatsApp systems. |
Inbox assignment/audit logs | Agent assignment, tags, SLA events | No | Yes | Business systems | Operational metadata needed for QA, audits, and SLAs; avoid storing message content in logs. |
Consent records | Opt‑in/opt‑out, channel source, timestamps | No | Yes | Business systems | Critical for compliance and WhatsApp rules; maintain durable, queryable records. |
Consent, opt-in/out, and lawful messaging on WhatsApp (GDPR)
Getting consent right on WhatsApp is both a WhatsApp policies requirement and a GDPR necessity. The most successful brands treat consent as a product experience: clear value exchange, transparent disclosures, easy opt-out, and robust record-keeping - implemented natively in WhatsApp private messaging through Trikon.
"84% of consumers are concerned about privacy and expect organizations to make it a priority." - Source
The rules of WhatsApp and GDPR lawful bases
Utility vs. marketing categories: WhatsApp templates are reviewed for policy compliance. Utility templates cover transactional or account-related updates; marketing templates include promotions and win-backs; authentication templates deliver OTPs. Use the correct category to protect Quality Rating and deliverability.
Lawful bases by use case:
Contract: messages necessary to perform a contract or pre‑contract steps requested by the user (e.g., order confirmations, support responses, appointment logistics).
Legitimate interests: limited service communications with a balancing test and easy objection (e.g., gentle appointment reminders). Document your assessment.
Consent: required for promotions, newsletters, and abandoned cart nudges. Make it specific to WhatsApp, granular, and easy to withdraw.
Approval process: Marketing and certain utility templates require WhatsApp approval. Keep language specific, truthful, and consistent with your consent capture.
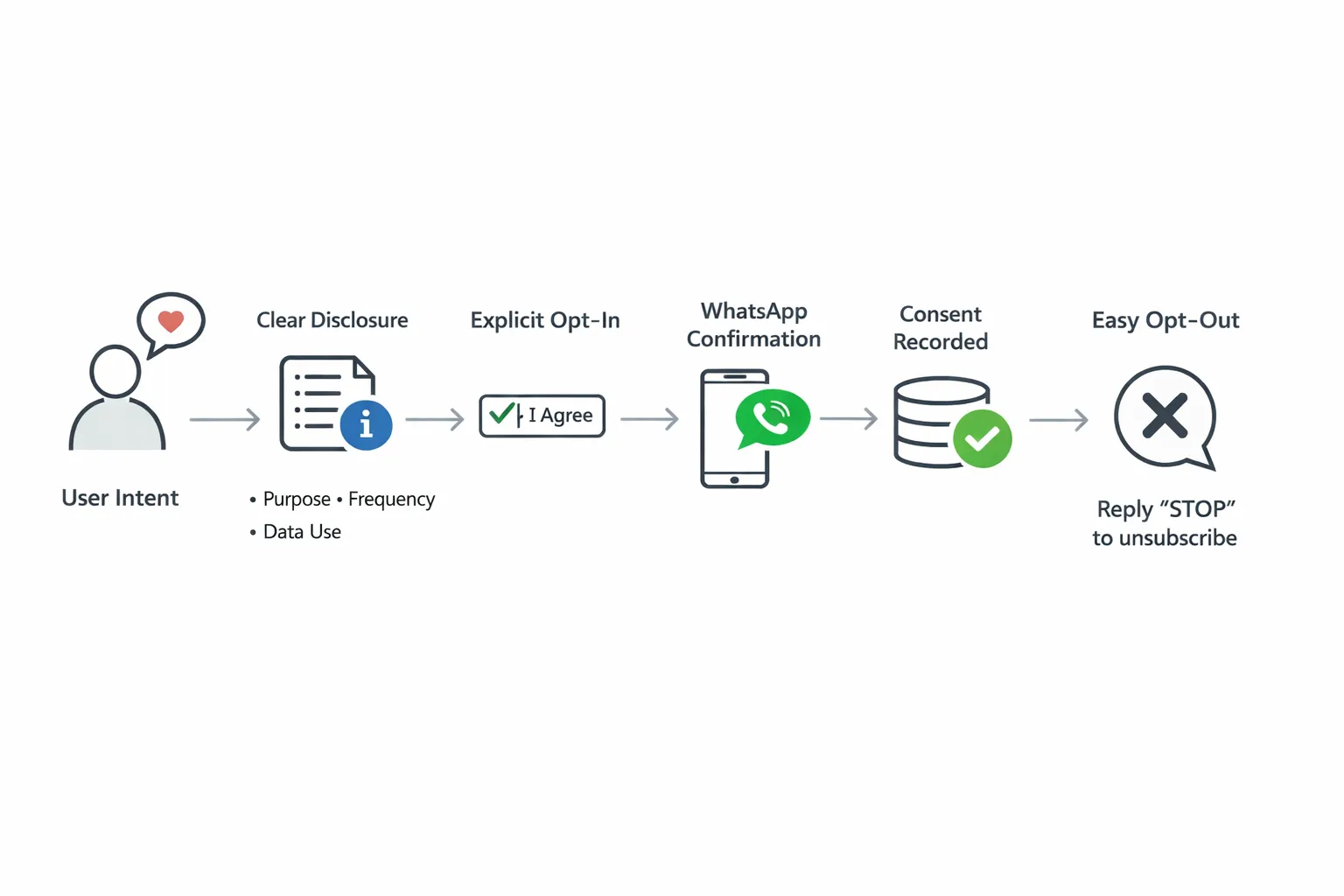
Collecting opt-in the right way
Channels: website forms/checkboxes, SMS capture, QR codes at POS, and click‑to‑WhatsApp ads (CTWA). Each must name WhatsApp explicitly and disclose purpose, frequency, data use, and opt‑out.
Double opt‑in: Confirm consent inside WhatsApp with a brief welcome message summarizing what the user will receive and how to opt out.
Preference centers: Let users manage topics, frequency, and quiet hours inside WhatsApp via quick replies/buttons.
Managing opt-out and suppression
Required commands: Respect “STOP”/“UNSUBSCRIBE” at the conversation level and across lists. Acknowledge instantly and confirm suppression.
List syncing: Sync suppression lists across CRM, CDP, and marketing tools to prevent re‑contact via WhatsApp private messaging.
Frequency capping and quiet hours: Cap marketing sends per user and enforce local quiet hours to avoid spammy experiences and protect your Quality Rating.
Record-keeping
Maintain a consent ledger: user identifier (phone/MSISDN), channel (WhatsApp), timestamp, source (form/CTWA/QR/POS), template/program name, policy version shown, and evidence (e.g., consent text, IP or POS terminal ID).
Log changes: consent updates, withdrawals, objections, and when suppression took effect.
Prove it: Your ledger should be queryable for audits, rights requests, and WhatsApp rules enforcement.
Lawful basis matrix for common WhatsApp use cases
Use case | Template category (utility/marketing/authentication) | Lawful basis | Is prior consent required? | Example opt-in copy | Opt-out wording | Retention guidance |
|---|---|---|---|---|---|---|
Order updates | Utility | Contract (necessary to fulfill order) | No (contractual necessity), but disclose channel use | “Send me WhatsApp order updates (shipping, delivery, issues) for this purchase.” | “Reply STOP to stop order updates on WhatsApp.” | Keep minimal order‑status records; delete message content after fulfillment + 90 days unless required for disputes. Retain consent note tied to the order record. |
Support chats | Session/Utility | Contract (pre‑contract/user‑requested support) | No prior consent for responding to user‑initiated chats; disclose privacy | “Contact me on WhatsApp to resolve my support request.” | “Reply STOP to end support messaging; we won’t message you unless you contact us.” | Retain chat transcripts only as needed for QA and disputes (e.g., 90–180 days). Mask PII in logs. |
Appointment reminders | Utility | Legitimate interests (balancing test) or Contract if service booked | Not if necessary for service; otherwise provide easy objection | “I’d like WhatsApp reminders and changes for my appointment.” | “Reply STOP to stop reminders; we’ll still notify you through your chosen primary channel.” | Keep reminder metadata briefly (e.g., 30–90 days). Document LI assessment. |
Abandoned cart nudges | Marketing | Consent | Yes | “I agree to receive WhatsApp reminders and offers about items in my cart.” | “Reply STOP to unsubscribe from WhatsApp marketing.” | Retain consent proof while active + audit window (e.g., 24 months after last use). Delete cart payloads quickly (e.g., 7–30 days). |
Promotions/newsletters | Marketing | Consent | Yes | “Send me exclusive offers and newsletters on WhatsApp. Frequency: up to 4/month.” | “Reply STOP to unsubscribe anytime.” | Keep consent ledger for program duration + audit window. Store campaign analytics without sensitive PII; aggregate when possible. |
OTP/authentication flows | Authentication | Contract (security of account) | No (user‑requested access), but disclose | “Use WhatsApp to send login codes and security alerts.” | “Reply STOP ALL to block non‑transactional messages; security alerts may continue via your backup method.” | Do not retain OTPs. Keep minimal delivery logs for fraud/security (e.g., 30–90 days). |
CTWA follow-ups | Utility → Marketing (if promotional) | Contract/Legitimate interests for response to inquiry; Consent for any marketing | Consent required for any promotional follow‑ups | “By tapping ‘Send’ you’ll receive a WhatsApp reply to your enquiry. For offers/news, opt in when prompted.” | “Reply STOP to opt out of marketing. For service-only messages, reply STOP ALL.” | Store conversation intent and timestamp (24‑hour window). Capture explicit consent before any marketing. Suppress upon STOP across systems. |
Trikon operationalizes these whatsapp privacy controls out of the box: compliant opt‑in capture across channels, policy‑aware templates, suppression syncing, quiet hours, and a durable consent ledger you can audit - so you meet GDPR and WhatsApp rules without slowing down growth.
Data handling, storage, and cross-border transfers
Building a compliant WhatsApp stack means minimizing data, securing what you must store, and documenting international transfers with the right safeguards - without slowing revenue teams down. Trikon helps you implement these controls out of the box.
Data minimization and purpose limitation
Collect only what’s necessary to fulfill a specific purpose (e.g., order status, appointment logistics). Avoid free‑text capture of special-category data in chat (health, biometrics, political views) unless strictly necessary and lawful.
Design for least privilege: restrict who can view PII in the shared inbox, mask sensitive fields in logs, and separate analytics from raw transcripts.
Define purpose‑bound retention: set granular timers for transcripts, media, and operational logs. Automate deletion or aggregation to reduce risk.
Where WhatsApp data lives in a business stack
User devices: Messages and media are end‑to‑end encrypted (E2EE) and stored on devices. Customers control their own chat history.
WhatsApp transport: Encrypted payloads are relayed for delivery; certain metadata supports routing, deliverability, and abuse prevention.
BSP platform (e.g., Trikon): Your operational layer for shared inbox, automation, chatbots, and campaigns. Apply encryption‑at‑rest, role‑based access, SSO/MFA, and audit logs.
CRM/data warehouse: Customer profiles, consent states, campaign performance. Use key management (KMS/HSM), field‑level encryption, and tokenization/pseudonymization for high‑risk attributes.
Security controls to standardize:
Encryption at rest: AES‑256 or stronger for databases and object storage.
Key management: Segregated KMS with rotation, separation of duties, break‑glass access workflows.
Tokenization: Replace sensitive identifiers (e.g., phone numbers) with tokens in downstream analytics.
Network controls: IP allow‑listing, private networking, and zero‑trust access for agents and integrations.
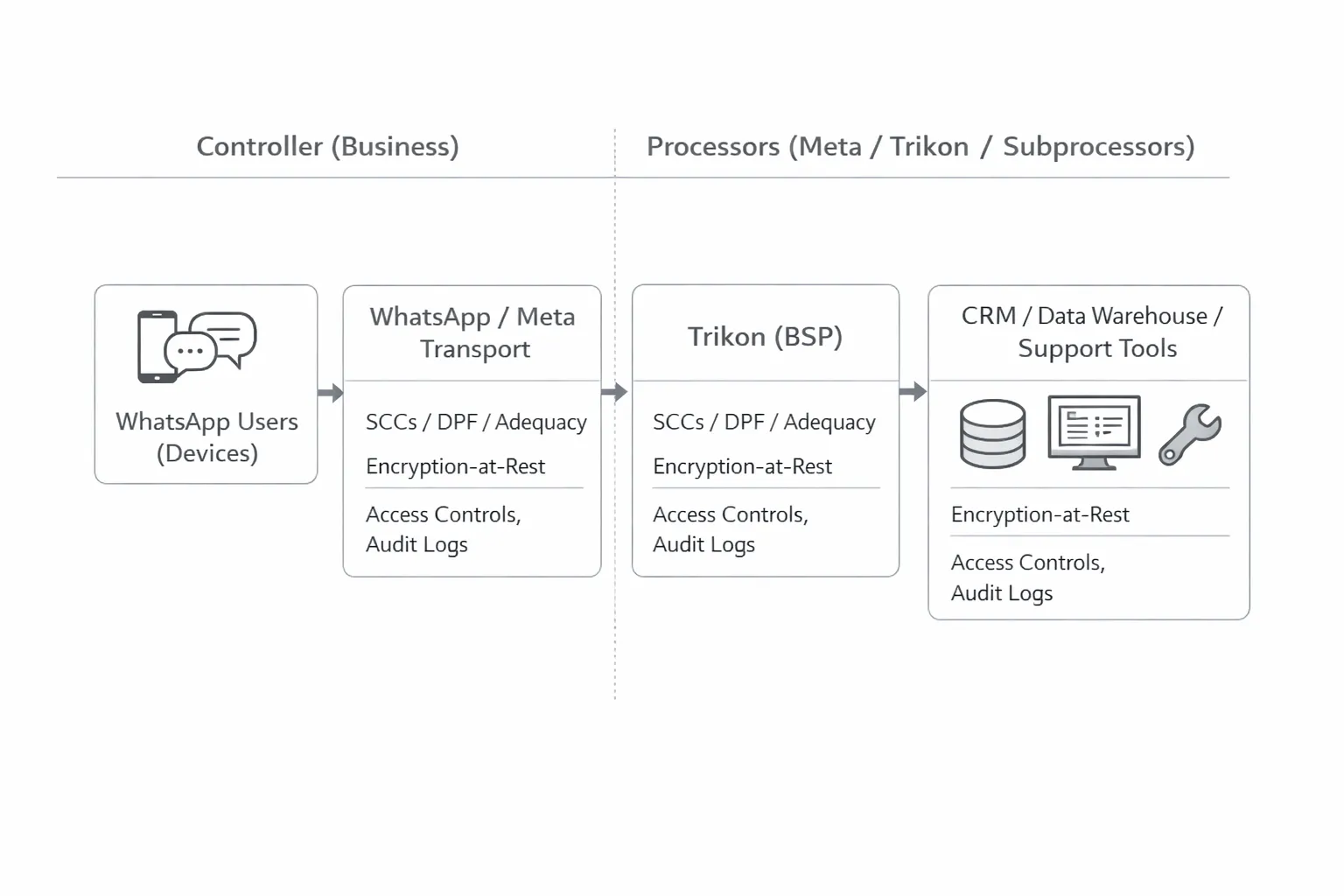
International transfers and safeguards
Transfer mechanisms:
Standard Contractual Clauses (SCCs) for most third‑country transfers and sub‑processors.
EU‑U.S. Data Privacy Framework (DPF) for certified entities.
Adequacy decisions (e.g., Israel) where recognized by the European Commission.
Practical steps:
Map vendors and sub‑processors handling WhatsApp data (Meta Cloud API, Trikon, hosting, analytics, support tools).
Conduct Transfer Impact Assessments (TIAs) for each third‑country transfer (scope, laws, access risk, supplementary measures).
Implement supplementary measures: strong encryption‑at‑rest with customer‑controlled keys, access controls, and event logging; minimize clear‑text exposure.
Keep records of processing and transfer logs for auditability.
"Cross‑border transfers rely on a combination of the EU‑U.S. Data Privacy Framework, adequacy decisions (e.g., Israel), and Standard Contractual Clauses." - Source
Data Processing Agreements (DPAs)
Roles and responsibilities: Clarify that your organization is the data controller; Meta (Cloud API), Trikon, and other platforms act as processors/sub‑processors.
Security annexes: Require encryption‑at‑rest, key management, access controls, logging, vulnerability management, and incident response SLAs.
Breach notifications: Define timelines (e.g., prompt notification, details required) and cooperation duties to support your regulatory obligations.
Audit rights: Ensure the ability to review third‑party reports (SOC 2/ISO 27001), request summaries of penetration tests, and conduct audits where appropriate.
Sub‑processor flow‑down: Processors must mirror core commitments with their sub‑processors and provide advance notice of changes.
Trikon operationalizes this with clear role definitions, SCC/DPF coverage where applicable, encryption‑first storage, and export‑ready records - so your WhatsApp data moves globally with documented safeguards and minimal risk.
Retention, deletion, and the ‘right to be forgotten’ in WhatsApp
A compliant WhatsApp program balances platform defaults with policy-driven retention and deletion in your business systems. Trikon helps you implement retention schedules, automate redaction, and action data subject requests (DSRs) without disrupting operations.
Platform defaults and features impacting retention
30‑day undelivered message window: Undelivered messages may be stored (encrypted) for up to 30 days for delivery attempts; then deleted. Design your workflows knowing transient delivery storage exists.
Disappearing messages: Useful to reduce exposure, but they do not replace your duty to honor lawful retention, deletion, and DSRs in connected business systems.
View‑once media: Limits re‑use and redistribution in-app. Avoid copying view‑once content into external systems unless strictly necessary and lawful.
Business retention strategy
Policy‑based retention: Define purpose‑based timers for transcripts, attachments, and operational metadata (e.g., 90–180 days for support transcripts; shorter for sensitive data). Automate purge/archival in CRM/inbox.
Redaction and minimization: Mask PII in logs and analytics. Strip unnecessary fields from exports, and tokenize phone numbers for BI.
Separate retention for consent and suppression: Keep consent and opt‑out records longer than message content to evidence lawful messaging, even after content deletion.
Deletion and DSR workflows
Supported rights: Access, rectification, erasure, objection, and portability. Document SLAs (e.g., respond without undue delay, typically within 30 days under GDPR).
Identity verification: Verify requestor identity (e.g., one‑time challenge to the WhatsApp number on file) before actioning erasure or export.
Data discovery: Search across Trikon inbox, automation logs, CRM/CDP, data warehouse, and backups. Minimize rehydration from backups - log justifications if restore is required.
Execution and confirmation: Apply deletion/redaction to active systems; queue backup lifecycle actions; confirm completion to the requester with scope and date.
Audit trails and evidence
Immutable logs: Track who performed what action (view, export, delete), when, and why - without storing unnecessary content in the log itself.
Evidence pack: Retain consent snapshots, opt‑out timestamps, DSR correspondence, and deletion job IDs for regulator inquiries.
Continuous testing: Run periodic deletion drills and retention audits; reconcile suppression lists across channels to prevent re‑contact.
Trikon provides configurable retention policies, redaction tooling, consent/suppression ledgers, and DSR workflows - so you can operationalize deletion and the right to be forgotten while protecting deliverability and customer trust.
Access governance, devices, and operational security
Operational security is what keeps whatsapp privacy real in day‑to‑day work. Trikon helps you enforce least‑privilege access, secure identities and devices, and harden APIs so your WhatsApp private messaging stays compliant with WhatsApp policies and data protection rules - without slowing your teams.
Roles and least-privilege in a shared inbox
RBAC by brand/team/queue: Segment access by business unit, geography, and queue (sales, support, VIP). Grant only the permissions each role needs (Agent, Supervisor, Analyst, Admin).
Conversation‑level permissions: Control who can view, assign, tag, export, or delete messages. Restrict bulk actions to supervisors/admins.
Maker‑checker for broadcasts: Require approval workflows for marketing sends and template changes. Pre‑flight checks for opt‑in coverage, quiet hours, frequency caps, and audience size.
SLA tracking for oversight: Use SLA policies and breach alerts to catch bottlenecks early. Supervisors see queue health, agent load, and quality metrics without needing PII access.
Auditable changes: Every sensitive action - role edits, permissions, exports, template activation - should be logged with who/when/why.
Identity, authentication, and session security
Enterprise SSO: Enforce SAML/OIDC SSO with conditional access (network, device posture, geo) for the Trikon workspace.
SCIM provisioning: Automate just‑in‑time user creation, deprovisioning, and group‑to‑role mapping. Immediate revocation closes insider‑risk gaps.
MFA/2FA policies: Enforce MFA for all staff; step‑up re‑auth for exports, API key creation, and role changes.
Session controls: Short inactivity timeouts, rotating tokens, device binding, and IP restrictions for high‑risk roles. Block concurrent sessions for shared terminals.
Device trust: Allow only managed browsers/OS versions; flag rooted/jailbroken/mobile emulators; require disk encryption and screen‑lock on endpoints.
API and webhook hardening
Scoped API keys: Issue per‑integration keys with least privilege (read‑only analytics vs. send permissions). Rotate keys on a schedule and on staff turnover.
Network controls: IP allow‑listing and optional mTLS for inbound API calls. Rate‑limit per key and per route to contain abuse.
Webhook verification: Sign outbound webhooks with HMAC‑SHA256 and include timestamp/nonce headers. Require your receivers to verify signatures and reject stale or replayed events.
Idempotency and replay protection: Require idempotency keys on write endpoints (sends, updates). Store recent keys and timestamps to block duplicates.
Secrets management: Store credentials in a KMS/HSM, never in code or logs. Enforce change control on environment variables and CI/CD pipelines.
Device and channel hygiene
Companion devices and web sessions: Monitor active WhatsApp web/companion sessions. Auto‑expire dormant sessions and allow supervisors to force‑logout on role changes.
Number ownership and rotation: Keep numbers owned by the business (not staff). Document SIM/number change procedures, sender name alignment, and customer notification plans. Set fallbacks for failover numbers.
Media handling: Disable local downloads by default on shared machines. Use secure links with short TTLs for attachments. Strip EXIF/location data where possible.
Environment separation: Isolate production from staging/sandbox numbers and data. Prevent test data from flowing into live audiences.
Anti-abuse and phishing defense
Template monitoring: Track quality rating, block rates, and opt‑out deltas by template and audience. Auto‑pause templates breaching thresholds; require review before re‑enable.
Domain verification and URL hygiene: Use verified sending domains and branded links. Scan URLs for reputation and enforce HTTPS. Avoid open redirects and unknown link shorteners.
Content safeguards: Flag risky phrases or PII leakage in agent‑typed messages. Require supervisor review for high‑reach or sensitive broadcasts.
Agent readiness: Run quarterly training on the rules of WhatsApp, social engineering, and data handling. Provide playbooks for suspected account takeover, spam spikes, and phishing reports.
Incident readiness: Maintain runbooks for compromised credentials, mis‑sends, and data exposure. Include rapid suppression, customer notification criteria, and regulator escalation steps.
Trikon brings these controls together - granular RBAC, SSO/SCIM, MFA, audit logs, approval gates for broadcasts, and hardened APIs - so your teams can scale WhatsApp operations securely and in line with whatsapp rules and regulatory expectations.
Messaging content policies and acceptable use (rules of WhatsApp)
Building trust in WhatsApp private messaging means staying inside both the rules of WhatsApp and applicable data protection law. Trikon helps brands enforce content standards, template governance, and compliant delivery - so your messages land, convert, and keep your Quality Rating healthy.
WhatsApp policies to respect
Prohibited content: No illegal goods/services, hate or harassment, adult/sexual content, weapons and explosives, unsafe supplements, or deceptive/financial scams. Ads or messages must not mislead or impersonate.
Regulated industries: Extra scrutiny applies to financial services, health, alcohol, tobacco, gambling, and prescription drugs. If permitted, provide compliant disclosures and link to terms; avoid collecting sensitive details in-chat unless strictly necessary and lawful.
Personal data minimization: Share only what is needed to fulfill the purpose (e.g., last 4 digits of an order vs. full payment data). Do not request full card numbers, SSNs, or medical histories in chat. Use view‑once for sensitive media and redact data in downstream systems.
Brand transparency: Clearly identify your brand in the template and first message, provide a direct opt‑out (“Reply STOP to unsubscribe”), and link to a privacy notice when appropriate.
Template quality and deliverability
Quality Rating health: WhatsApp evaluates user feedback (blocks/reports), spam signals, and engagement. Low quality can throttle or suspend marketing templates. Keep copy clear, personalized, and genuinely useful.
Rate limits and tiers: Messaging limits scale with good standing. Ramp gradually, watch complaint rates, and avoid sudden spikes in new audience sends that can trigger protections.
Avoid spammy patterns:
Overuse of ALL CAPS, excessive emojis, and pushy CTAs.
Repetitive reminders with no new value.
Bait‑and‑switch or misaligned content vs. opt‑in.
Continuous monitoring in Trikon: Track Quality Rating shifts, block/report deltas, link health, and opt‑out spikes per template and segment. Auto‑pause offenders and require supervisor review before re‑enable.
Frequency, relevance, and quiet hours
Preference‑based scheduling: Honor stated frequency (e.g., “up to 4/month”) and topic choices (orders vs. promos). Provide an easy way to change preferences inside WhatsApp.
Segmentation: Send only to opted‑in audiences by interest, lifecycle stage, and location. Exclude non‑responders or recent opt‑outs across all lists with real‑time suppression sync.
Throttling and pacing: Ramp to new cohorts, cap daily sends per user, and space reminders. Use send windows that align with local time zones.
Quiet hours: Respect local quiet hours and do-not-disturb windows to reduce complaints and protect deliverability. Trikon enforces quiet hours at workspace, brand, or campaign level.
Special categories and minors
Sensitive data: Avoid collecting or storing special‑category data (health, biometrics, religious beliefs, sexual orientation) in chat. If there is a lawful need, use the minimum necessary, prefer view‑once, and enforce strict retention with redaction.
Minors and age‑gating: Where required, use age gates before promotional messaging and avoid profiling minors. Obtain parental consent when legally required and limit data collection to essentials.
Safety‑first templates: For service updates to minors or sensitive segments, keep copy factual, neutral, and free from upsell prompts. Provide help links and easy opt‑out.
How Trikon helps you stay compliant with WhatsApp rules:
Policy‑aware template reviews and approval workflows (maker‑checker).
Automated opt‑in/opt‑out handling with suppression syncing and quiet hours.
Quality Rating dashboards, alerting, and auto‑pause safeguards.
PII minimization tools, view‑once and disappearing‑message support, and redaction in exports/logs.
Role‑based access, audit trails, and content guardrails for agents and automation.
Measurement and monitoring: prove privacy compliance
Privacy isn’t just a policy; it’s a measurable program. To keep WhatsApp private messaging compliant and performant, you need clear KPIs, auditable evidence, disciplined risk reviews, and tested incident playbooks. Trikon centralizes these controls - so you can prove compliance and protect deliverability at scale.
KPIs to track
Opt-in rate
Definition: unique opt-ins ÷ unique invitation opportunities per channel (web form, CTWA, QR, POS).
Why it matters: demonstrates lawful basis and value exchange for whatsapp privacy; higher rates correlate with quality templates and disclosures.
Tips: A/B test disclosures, purpose clarity, and frequency promises; separate rates by source to find top-performing acquisition paths.
Opt-out rate
Definition: unique opt-outs ÷ messages sent (by template/program/segment).
Why it matters: early warning for content misalignment and rules of WhatsApp violations; guardrail for frequency and quiet hours.
Tips: track 24–48h post-send spikes; auto-pause templates crossing your threshold (e.g., ≥0.5–1%).
Complaint/block rate
Definition: blocks/reports ÷ messages sent (by template and audience).
Why it matters: directly impacts Quality Rating and deliverability; critical for whatsapp policies adherence.
Tips: correlate with send time, copy, and audience freshness; throttle or re‑target only engaged cohorts.
Delivery/read rate
Definition: delivered/read confirmations ÷ messages sent.
Why it matters: reveals list health, device status, and template relevance; reads are a strong proxy for experience quality.
Tips: segment by device locale and send window; remove inactive numbers to protect sender reputation.
Conversion
Definition: attributed business outcome (purchase, booking, payment, NPS response) ÷ messages sent/read.
Why it matters: ensures privacy-first messaging still drives outcomes; funds the program while staying inside whatsapp rules.
Tips: attribute with privacy-safe UTMs, server events, or in‑chat actions; avoid PII-heavy attribution.
Additional privacy-specific health metrics:
Consent coverage: percent of active audience with valid, channel-specific opt-in and up-to-date purpose tags.
Suppression integrity: zero sends to suppressed numbers across systems (CRM/CDP/BSP).
Retention SLA: percent of records deleted/redacted on schedule (content vs. consent ledger).
Access exceptions: count and age of unresolved role/access deviations.
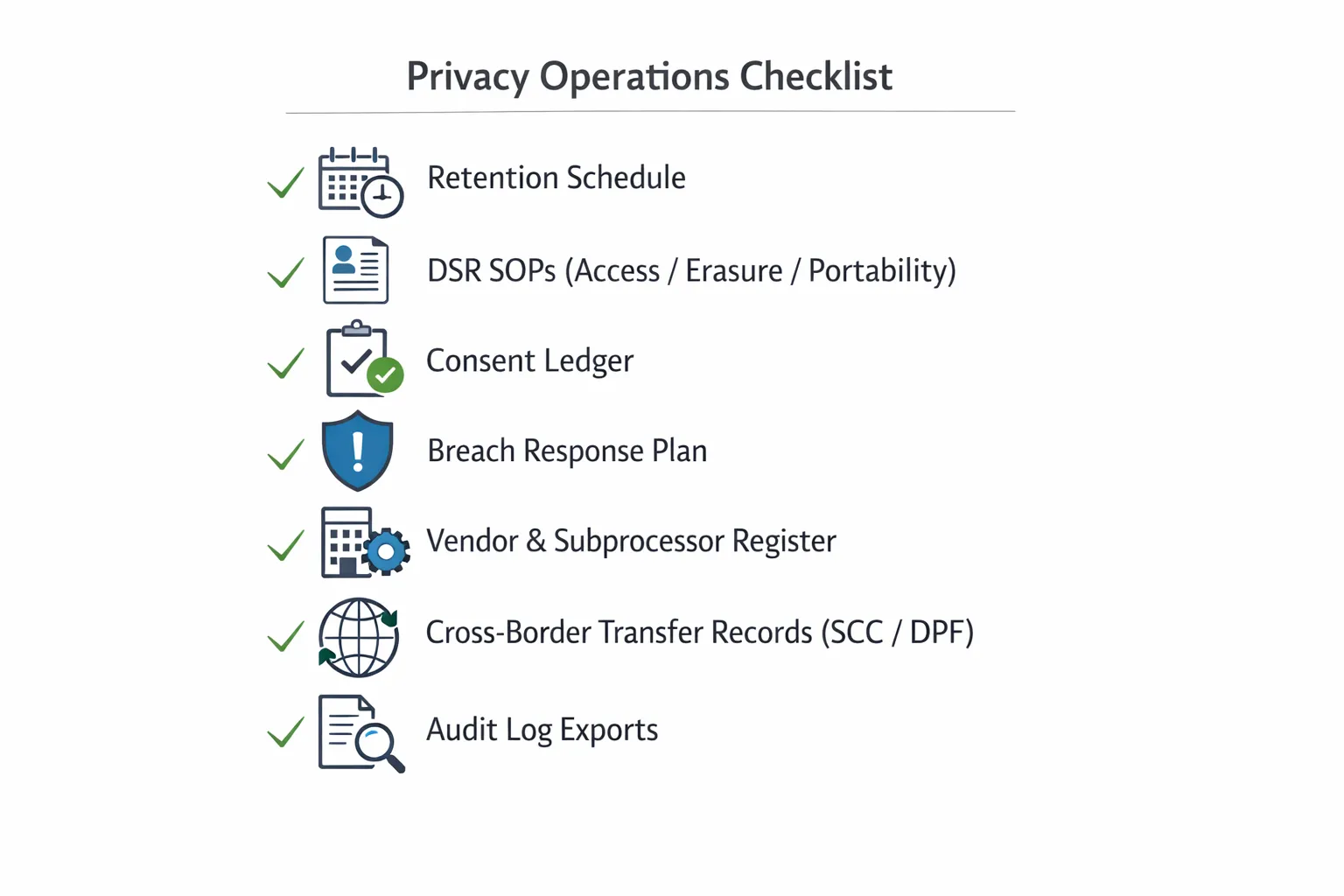
Evidence and audit readiness
Consent ledger integrity
Store: MSISDN, channel=WhatsApp, purpose, frequency promise, timestamp, source (CTWA/QR/web/POS), policy/version, proof text.
Controls: immutability for original consent; change-log for updates and withdrawals; easy export for regulators.
DSR turnaround time
Track SLA: access/erasure/objection/portability completion time, verification method, systems touched, residual backup handling.
Drill: monthly spot checks with redaction tasks and cross-system deletes (inbox, CRM, warehouse, backups).
Access review cadence
Quarterly RBAC reviews: least-privilege checks by brand/team/queue; evidence of revocations and SCIM deprovisioning.
Sensitive actions: export/send/template changes require maker‑checker and appear in audit logs with who/when/why.
Regulator-ready package
Contents: RoPA (records of processing), transfer map (SCC/DPF/adequacy), vendor/subprocessor register, Quality Rating history, suppression proof, audit log exports.
DPIA/PIA cadence and triggers
When to initiate:
New automations (e.g., abandoned cart or retargeting flows), new data categories (special/sensitive), new markets (EEA/UK/BR/SG), or new vendors/subprocessors.
What to document:
Data flows (controller/processor roles), lawful bases per use case, consent language, retention schedules, security controls (E2EE context, encryption-at-rest, key management).
Risk assessment: balancing test for legitimate interests, residual risk, and mitigations (view‑once, disappearing messages, masking).
Sign-offs and review:
Legal, security, marketing owners; versioning and next review date (e.g., annual or upon material change).
Trikon support:
Exportable data flow diagrams, consent text snapshots, template catalogs, retention configurations, and audit logs for the annex.
Incident response drills
Playbooks to maintain
Mis-send broadcast (wrong audience/quiet hours breach).
Compromised credential/API key or unauthorized device session.
PII leakage in chat/export; improper data retention.
Tabletop exercises
Frequency: at least semiannual; rotate scenarios across marketing, support, and engineering.
Objectives: measure MTTD/MTTR, validate suppression blast radius, confirm legal/comms alignment.
Regulator/customer communications templates
Include: incident summary, affected data types, timeframes, mitigations, user steps, and regulator-specific notices (e.g., GDPR 72‑hour notification triggers).
Channel readiness: pre-approved WhatsApp and email templates that meet whatsapp policies and avoid further exposure (no sensitive details in notifications).
Evidence of readiness
Drill reports, post‑mortems with action items, remediation tracking, and updated runbooks in your audit pack.
How Trikon helps
Privacy and deliverability dashboards: opt‑in/opt‑out, block/complaint, Quality Rating, delivery/read, and conversion by template and segment.
Consent/suppression integrity: real-time sync across systems, quiet hours enforcement, auto‑pause on threshold breach.
Audit exports: consent ledger, template history, RBAC changes, DSR workflows, and retention execution logs - ready for internal audit or regulator review.
How Trikon delivers WhatsApp privacy by design
Trikon turns WhatsApp private messaging into a compliant, conversion-ready channel. Every capability is built to honor WhatsApp policies and the rules of WhatsApp while meeting data‑protection expectations - so teams can scale revenue without risking trust.
Consent-first marketing automation
Built-in opt‑in capture: Collect explicit, channel‑specific consent from website, CTWA, QR, or POS - with purpose tags, frequency promises, and policy versioning.
Suppression lists that actually sync: Real‑time suppression across broadcasts, drips, and retargeting flows prevents re‑contact and protects your Quality Rating.
Frequency caps and quiet hours: Enforce per‑user caps, local‑time quiet hours, and audience cooling‑off windows to avoid spammy patterns and blocks/reports.
Policy‑aware templates: Maker‑checker approvals and linting for template copy, links, and variables; checks for consent coverage and audience eligibility before send.
Segmentation by consent: Target only users with valid WhatsApp opt‑in, purpose alignment (utility vs. marketing), and up‑to‑date preferences.
Centralized Support Inbox with governance
RBAC and least privilege: Role‑based access by brand/team/queue; restrict export/delete rights; vault sensitive threads; masked PII in search and logs.
Agent assignment and SLA tracking: Route by skills/priority and monitor SLA breaches without exposing unnecessary personal data.
Full conversation history with retention controls: Redact at message/field level, set policy timers per queue (e.g., support vs. VIP), and auto‑archive completed cases.
Immutable audit logs: Who viewed/exported/edited templates, who approved a broadcast, when suppression changed - every action is traceable.
DSR workflows: Locate, export, and erase WhatsApp records across inbox, automations, and integrations - complete with requester verification and evidence trail.
No‑code chatbots with human handoff
24×7 automation for FAQs: Keyword/AI logic handles repetitive questions while respecting whatsapp privacy by minimizing data capture.
Escalation rules that respect consent: Seamless agent handoff with context sharing; sensitive intents can auto‑switch to view‑once or request offline channels.
PII redaction controls: Mask numbers, emails, and order IDs in bot transcripts and analytics; control which entities the bot is allowed to collect.
Safety guardrails: Block risky phrases, unapproved links, or template misuse; require supervisor review for high‑impact bot responses.
Bookings, operations, and commerce in chat
Appointments and reservations: Utility‑template flows for confirmations, reminders, and changes - all mapped to proper lawful basis.
Payments and secure checkout: Fast, compliant paths that minimize exposure of payment data (tokens/links, not raw PANs) and respect quiet hours.
WhatsApp storefront: Catalogs, carts, and orders integrated with your e‑commerce - opt‑in aware retargeting (e.g., abandoned cart) and suppression‑safe win‑backs.
Operational updates done right: Delivery/ETA, service notifications, and post‑service feedback sent via utility templates with purpose‑bound retention.
Reliability and compliance at scale
Official WhatsApp Business API partner: High deliverability, monitored quality ratings, and template performance insights to protect sender reputation.
Export and retention controls: One‑click exports for audits (consent ledger, template history, RBAC changes) and policy‑driven deletion for transcripts/media.
Security by default: Encryption at rest, role‑scoped API keys, IP allow‑listing, HMAC‑signed webhooks, and event replay protection.
White‑label for agencies: Separate workspaces, brand‑level policies, and audit‑ready evidence packs for your clients.
Faster go‑live
Minimal setup, no engineering: Skip complex flow builders - launch compliant support, broadcasts, and bots in days, not months.
Opinionated best practices: Prebuilt templates, consent copy, quiet hours, and suppression defaults tuned to WhatsApp rules and whatsapp privacy messages.
Scalable from day one: Add queues, brands, and markets with standardized RBAC, retention, and DPIA‑ready documentation.
Trikon operationalizes privacy‑by‑design on WhatsApp - so your teams can market, support, and sell with confidence, prove compliance on demand, and keep customers coming back.
Conclusion: Keep WhatsApp private and compliant with Trikon
WhatsApp private messaging can be both safe and high‑performing when privacy is designed into the workflow. End‑to‑end encryption (E2EE) protects message content in transit; your responsibility is everything around it - consent, data minimization, retention, access, and auditability. With Trikon, you operationalize whatsapp privacy from day one, align with the rules of WhatsApp, and turn compliance into a growth advantage.
The bottom line
E2EE protects message content; your policies protect everything else.
With the right consent, retention, and access controls, WhatsApp can be a safe, revenue‑driving channel.
Trikon embeds governance across marketing, support, chatbots, bookings, and commerce - so your whatsapp privacy messages stay compliant with WhatsApp policies and data protection law.
Next step
Start your privacy‑first WhatsApp program with Trikon: faster go‑live, built‑in compliance guardrails, and measurable growth.
Visit https://whatsapp.trikon.tech/ to book a demo.

